eduroam at North Geelong Secondary College

eduroam is short for “education roaming”.
eduroam is a global service enabling staff and students of educational, research and related institutions to visit another eduroam participating institution and connect to the visited institution’s wireless network automatically, i.e. with minimal effort for both user and visited institution.
eduroam infrastructure provided by North Geelong Secondary College, AARNet and global participants enables a North Geelong Secondary College visitor’s ‘home institution’ to authenticate the visitor remotely. Upon successful authentication, North Geelong Secondary College grants wireless network access to the visitor. Other eduroam participating institutions similarly grant network access to visiting users from North Geelong Secondary College.
If configured correctly, eduroam users should be able to get a network connection at a visited institution just by opening their laptop or activating their phone or tablet device.
More about eduroam is available from AARNet, the eduroam AU ‘roaming operator’.
eduroam
Explore how eduroam works.
eduroam Policy
Trust in eduroam authentication is underpinned by use of a proven secure technical infrastructure and protocol, and a set of policies to which all eduroam participants are required to comply.
In participating in eduroam AU, North Geelong Secondary College agrees to conform to the Global eduroam Policy and the eduroam AU policy maintained by AARNet.
What is the users’ responsibility in using eduroam?
The eduroam AU policy states that users must conform to their home institution’s network Acceptable Use Policy (AUP).
Users are recommended to read and comply with the Acceptable Use Policy of visited institutions. Visiting eduroam users should refer to North Geelong Secondary College AUP.
What about user privacy?
When using eduroam, the eduroam protocol prevents your institutional password from being revealed to any eduroam server other than your home institution’s eduroam server. So your login password is protected and remains secret between you and your home institution.
However your username is visible to the North Geelong Secondary College RADIUS server and other eduroam infrastructure servers involved in getting your authentication request from your device to your home institution, and may be included in logs. Such logs are required to be protected by the institution running the RADIUS server.
NGSC’s Wireless Settings
| SSID (Network Name) | eduroam (case-sensitive) |
| Wireless Network Connection Protocol | WPA2 Enterprise |
| Data Encryption Method | AES |
North Geelong Secondary College Users using eduroam
North Geelong Secondary College users should configure eduroam authentication locally (i.e. while on North Geelong Secondary College campus) and confirm successful authentication by North Geelong Secondary College eduroam infrastructure before travelling to other eduroam participating institutions.
Authentication Configuration
The following authentication parameters apply for authentication of North Geelong Secondary College staff via eduroam (below assumes the realm is ngsc.vic.edu.au):
| Security | WPA2-Enterprise |
| Encryption | AES |
| EAP Method | PEAP |
| Inner Method | MSCHAPV2 |
| Identity | <NGSC username>@ngsc.vic.edu.au |
| Anonymous Identity | Do not configure an anonymous identity |
| CA Certificate | Will auto-detect |
Visitors Using eduroam at North Geelong Secondary College
Who can use eduroam at North Geelong Secondary College?
eduroam is available to general staff, academics, researchers and students from eduroam participating educational, research and related institutions globally.
How do I use eduroam at North Geelong Secondary College?
Note: as an eduroam user, you should have already configured access to eduroam while on your home campus, using the authentication parameters provided by your home institution local eduroam webpage.
The wireless encryption protocol used by North Geelong Secondary College access points is the WiFi standard “WPA2/AES” (also called WPA2 Enterprise). Accessing eduroam successfully within North Geelong Secondary College requires only that your device’s configured wireless network connection and encryption protocol is compatible. Due to near-ubiquity of “WPA2/AES” support by institutional wireless access points, it is pretty much guaranteed that your wireless connection will be configured correctly if you’ve already tested your eduroam authentication on your own campus.
Note: There is no need to change any of your authentication parameters. These are only relevant to your home institution. If you have successfully configured authentication to eduroam at your home institution, you should be able to access North Geelong Secondary College campus’s network via eduroam with no change to your setup.
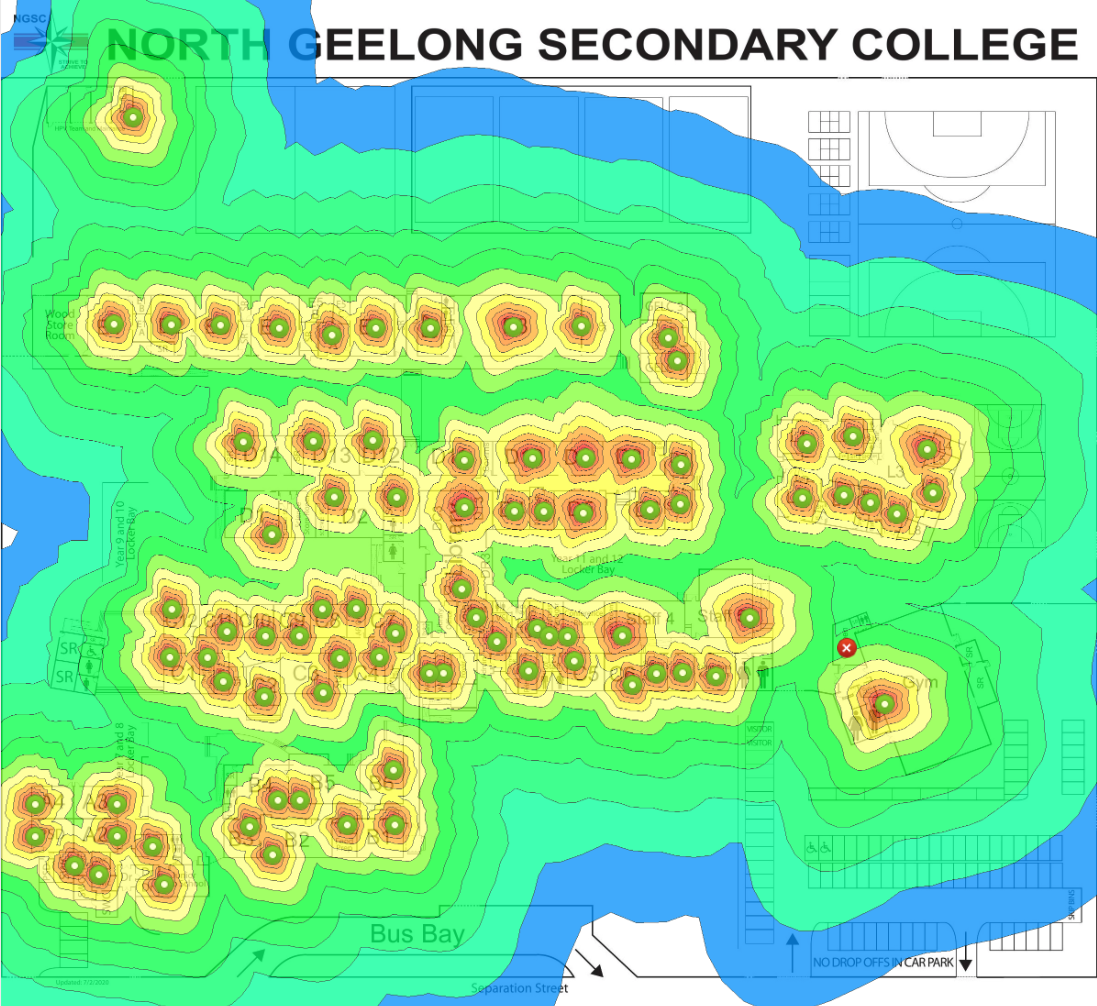
Where exactly can I use eduroam within NGSC?
North Geelong Secondary College provides eduroam at the following locations:
- eduroam coverage map for NGSC
Network Services Provided
North Geelong Secondary College provides full outbound access with NAT’ed IP addresses. In other words, you can access any services you normally do e.g. the Internet, your institution via VPN etc. However any servers running on your devices will not be accessible externally while connected to the North Geelong Secondary College network.
How do I get support in using eduroam?
When you’re on a North Geelong Secondary College campus and connect to eduroam, due to relative complexity of wireless and eduroam infrastructures, you may experience difficulty in getting a network connection due to several reasons e.g. an issue with your device configuration, wireless networking, institutional eduroam operability or eduroam infrastructure operability.
If network access issues occur, in the first instance eduroam users should contact their home institution’s IT helpdesk to seek support.
If this is not possible, or if the home institution can’t resolve the issue, visiting users may contact the North Geelong Secondary College IT support (phone, email).
If required, your home institution’s or North Geelong Secondary College eduroam support staff will contact AARNet, the eduroam AU national roaming operator, for additional assistance.
What Usage Logs are kept by North Geelong Secondary College and what are they used for?
The eduroam trust model (between institutions remotely authenticating their users, and other institutions providing network access, via eduroam) is supported by the ability to trace a particular network access event to an authentication of a ‘real user’ by their home institution.
Home institutions agree to take appropriate action on behalf of visited institutions in case a user doesn’t comply with the home institution’s network AUP.
In order to provide this traceability, remote authentication and network access transactions via eduroam are logged by North Geelong Secondary College, with logs being retained for a period of six months. Access to usage logs is restricted to authorised personnel and authorities as required by the law.
Usage logs may also be used for purposes of service trouble-shooting and user support.













